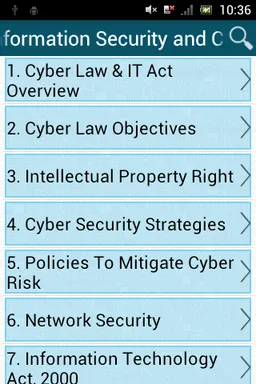
Information Security and Cyber Law
Pham Thuy · ict.tutorial.informationsecurityandcyberlaw



UpdatedOct 31, 2024
PublishedSep 11, 2019
Packageict.tutorial.informationsecurityandcyberlaw
MD5fac3593ded5224858c948cf34b271c5f
SHA1 (signer)29:91:0A:16:E4:73:8E:1F:C3:ED:49:8E:AE:61:0C:6F:9D:5F:D5:07
Signed byCN=Nguyen Thai Hoang, OU=OpLai, O=OpLai, L=Hanoi, ST=Hanoi, C=84
Malware scanUNKNOWN
Description
Anyone using a computer system and Internet to communicate with the world can use this tutorial to gain knowledge on cyber laws and IT security.
The Internet has now become all-encompassing; it touches the lives of every human being. We cannot undermine the benefits of Internet, however its anonymous nature allows miscreants to indulge in various cybercrimes. This is a brief tutorial that explains the cyber laws that are in place to keep cybercrimes in check.
In addition to cyber laws, it elaborates various IT Security measures that can be used to protect sensitive data against potential cyber threats.
The Internet has now become all-encompassing; it touches the lives of every human being. We cannot undermine the benefits of Internet, however its anonymous nature allows miscreants to indulge in various cybercrimes. This is a brief tutorial that explains the cyber laws that are in place to keep cybercrimes in check.
In addition to cyber laws, it elaborates various IT Security measures that can be used to protect sensitive data against potential cyber threats.
Required features
- Screen Portrait android.hardware.screen.portrait
- Touchscreen android.hardware.touchscreen
- Wifi android.hardware.wifi
Permissions (4)
Information Security and Cyber Law requests the following Android permissions:
- Access Network State android.permission.ACCESS_NETWORK_STATE
- Access Wifi State android.permission.ACCESS_WIFI_STATE
- Internet android.permission.INTERNET
- Write External Storage android.permission.WRITE_EXTERNAL_STORAGE