


UpdatedOct 10, 2020
PublishedOct 10, 2020
Packagenet.seesaa.sweet_baked_pie.AVR_discode
MD5b3e98acd53fafd589907b068eec6e6a3
SHA1 (signer)EC:E1:C8:8A:20:EB:9D:40:EC:08:C0:40:43:D9:09:C5:14:DF:B7:2B
Signed byCN=sweet_baked_pie, OU=Unknown, O=Unknown, L=Unknown, ST=Tokyo, C=JP
Malware scanTRUSTED
Contact[email protected]
What's new
v1.1
- Supported all AVR 8bit MCUs.
- Removed the advertisement.
- Reduced memory usage.
- Supported all AVR 8bit MCUs.
- Removed the advertisement.
- Reduced memory usage.
Description
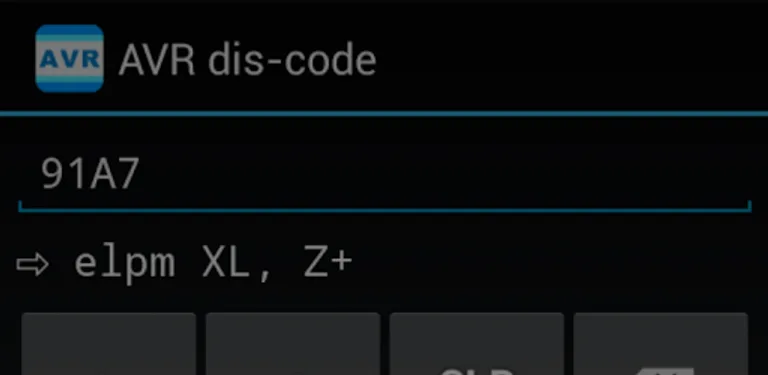
This app dis-codes a 16bit machine code of AVR microcontrollers to mnemonics.
FEATURES
- Supported all AVR 8bit MCUs.
- Supported exclusive instruction set (lds16/sts16) for AVR8L core.
- Not a dis-assembler.
FEATURES
- Supported all AVR 8bit MCUs.
- Supported exclusive instruction set (lds16/sts16) for AVR8L core.
- Not a dis-assembler.
Required features
- Faketouch android.hardware.faketouch